Another security threat is looming overhead for Internet and Bitcoin users around the world. The Network Time Protocol, commonly used to ensure electronic devices’ internal clocks are properly synchronized, is vulnerable to tampering. Considering how the communication between a device and the Network Time Protocol is almost never encrypted, a man-in-the-middle-attack becomes highly likely.
Also read: P2P Car Rental Service CarAmigo Reaches Taxation Agreement With Belgian Government
Network Time Protocol Vulnerability of Great Concern
In this day and age, any form of unencrypted communication is a major security risk. Especially when we are talking about services used by nearly every computer in the world today, such as the Network Time Protocol. Hackers can remotely reset devices’ clocks and dates, which could have catastrophic events for companies and users all over the world.
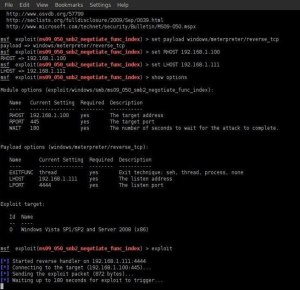
Picture the following scenario; a hacker manages to exploit the unencrypted Network Time Protocol communication with a major computer that receives regular updates. If the hacker wanted to, he could shift back the time and date to years ago. Doing so would prevent the system from receiving updates, making it vulnerable to exploits. For individual users, this might not seem like a major threat, but when companies are being targeted, the scenario changes dramatically.
To make matters even worse, encrypted traffic is not safe from prying eyes either once the Network Time Protocol has been exploited. Domain name system records could easily be tampered with, and HTTPS encryption can be bypassed in a simple manner. But that is not all, as Bitcoin users are not safe from harm by any means.
Bitcoin Users Vulnerable To Attack
All it takes for a hacker to attack a Bitcoin user is to shift time back by a few hours, rather than days or even years. Legitimate blockchain transaction entries could end up being rejected by Bitcoin users who are under attack from hackers, which would cause havoc on the blockchain and most services attached to it.
Note from the author: In theory, Network Time Protocol prevents device time changes of more than 16 minutes. This makes it an unlikely method to attack Bitcoin users, yet it could only be a matter of time until hackers find a way to bypass this “limit” as well.
While it may seem rather easy to spot a tampered computer or other device, the Network Time Protocol vulnerability could still cause havoc in limited environments. Or as is more likely to be the case, it will become an additional tools for hackers to try and exploit weaker systems and devices, to set up other exploit attempts.
That being said, it is all but impossible to ensure computers and communicating with legitimate Network Time Protocol Servers. Symmetrically encrypting the traffic is one option, although obtaining a key from the National Institute of Standards and Technology is a difficult task. Other encryption options could be used as well, yet hardly any of the services support those.
What are your thoughts on this Network Time Protocol vulnerability? Will it affect Bitcoin users in your opinion? Let us know in the comments below!
Source: Attacking the Network Time Protocol
Images courtesy of Shutterstock, Wikimedia, Nul-byte