CryptoCurrency Clipboard Hijackers — malware which replaces cryptocurrency wallet addresses with attacker’s addresses via Windows’ copy and paste mechanism — are not particularly new. However, one new sample has been discovered which monitors more than 2.3 million cryptocurrency addresses.
Clipboard Hijacking on the Rise
Nobody ever called cryptocurrency ‘user-friendly.’ (Or, if they did, they were wrong.)
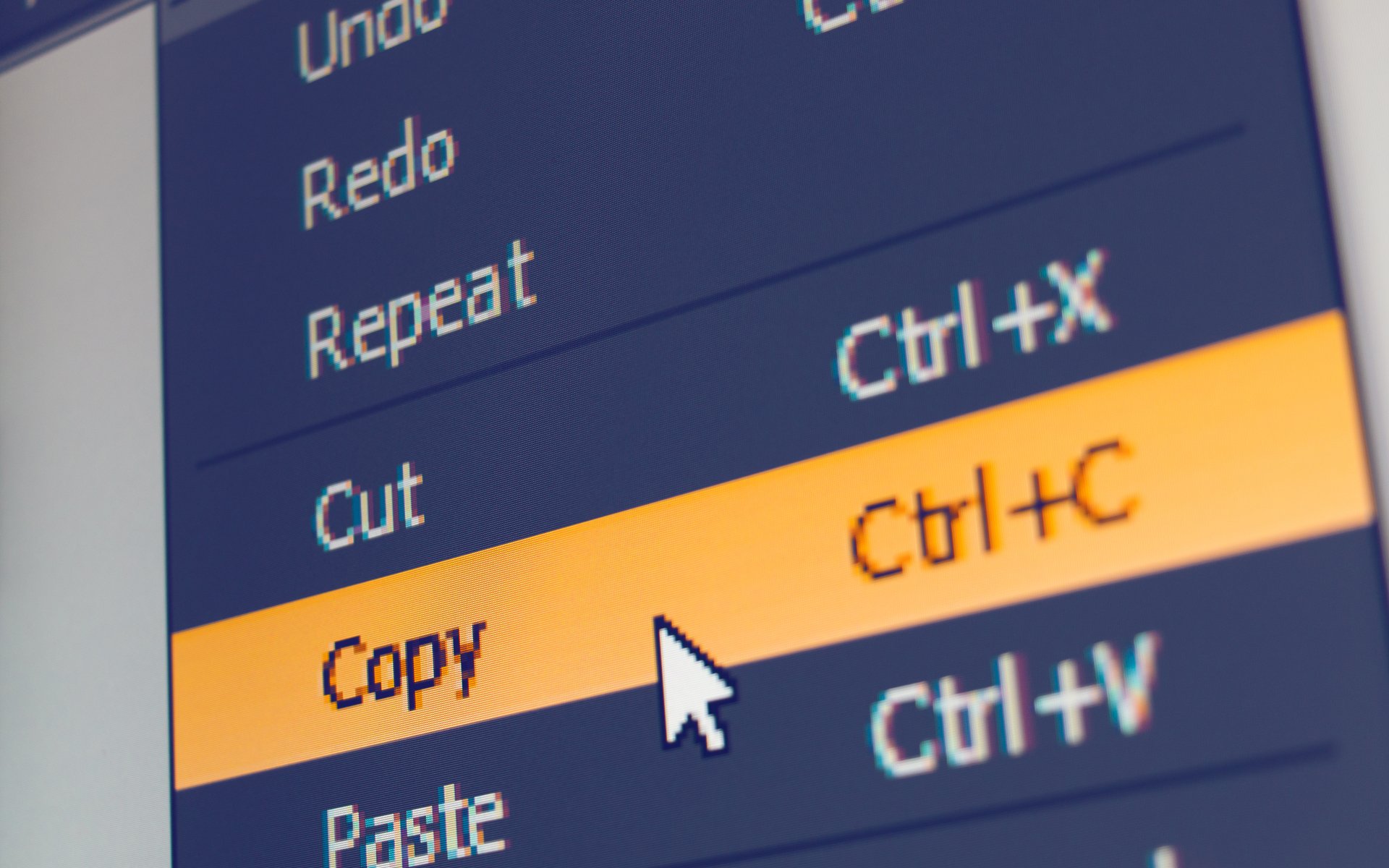
In the vast majority of cases, transacting cryptocurrencies requires inputting the receiver’s wallet address, which is comprised of a long and virtually impossible to memorize series of numbers and letters. To make their lives easier, most people copy and paste the address using their operating system.
If there’s a way to exploit something, hackers will figure it out — and the same applies here. Bitcoinist reported in April that malware identified by Palo Alto Networks targeted data held on user clipboards from the cut, copy and paste actions. That specific trojan was called ComboJack and replaced unsuspecting user’s wallet data with the wallet address of an attacker.
Most cases of CryptoCurrency Clipboard Hijackers were limited to less than a thousand cryptocurrency addresses. However, BleepingComputer has now discovered an example of this malware that monitors more than 2.3 million cryptocurrency addresses.
Explains the computer help website:
This infection was spotted as part of the All-Radio 4.27 Portable malware package that was distributed this week. When installed, a DLL named d3dx11_31.dll will be downloaded to the Windows Temp folder and an autorun called “DirectX 11” will be created to run the DLL when a user logs into the computer.
This DLL will be executed using rundll32.exe with the “rundll32 C:Users[user-name]AppDataLocalTempd3dx11_31.dll,includes_func_runnded” command.
Protecting Your Funds
As is the case with most malicious software, most infected users do not even realize they are infected until it’s too late.
To defend against such malware and avoid losing your cryptocurrency funds to malicious actors, it’s important to keep your antivirus software and operating system up-to-date.
Furthermore, cryptocurrency users should always — and we mean always — double-check any addresses when transacting cryptocurrencies. A simple way to handle this is to only check the first handful of characters and the last handful of characters in a given wallet address. However, checking every character letter-by-letter is the best way to ensure you’re sending to the right address.
What do you think about the latest findings that 2.3 million cryptocurrency addresses are being monitored by one sample of CryptoCurrency Clipboard Hijacking malware? Let us know your thoughts in the comments below!
Images courtesy of Shutterstock.