Microsoft has defended itself in the aftermath of WanaCry, saying system modernization is “a high priority for everyone.”
NSA, Consumers Firmly To Blame
As the Windows attack, known by various names such as WanaCry, WannaCrypt and WanaCrypt0r 2.0, rages on, the computer giant also pointed the finger firmly at the US National Security Agency (NSA). Microsoft president and chief legal officer Brad Smith write in a blog post on Sunday:

The WannaCrypt exploits used in the attack were drawn from the exploits stolen from the National Security Agency, or NSA, in the United States. That theft was publicly reported earlier this year.
This, Edward Snowden subsequently noted, is effective confirmation that the NSA lay at the source of the attack.
Extraordinary: Microsoft officially confirms @NSAGov developed the flaw that brought down hospitals this weekend. https://t.co/zQ6785YpFf
— Edward Snowden (@Snowden) May 14, 2017
At the same time, Microsoft’s position on business consumers was clear, if tempered: operating legacy systems was beyond its control, and organizations themselves only have themselves to blame:
As cybercriminals become more sophisticated, there is simply no way for customers to protect themselves against threats unless they update their systems. Otherwise they’re literally fighting the problems of the present with tools from the past […] This attack is a powerful reminder that information technology basics like keeping computers current and patched are a high responsibility for everyone, and it’s something every top executive should support.
Windows XP Legacy At Risk The World Over
As major victims such as Telefonica and the UK’s National Health Service scrabble to regain full control, the attack is continuing to spread, especially in China, where up to 29,000 businesses have now become affected.
Any significant system with older Windows operating systems at its core – specifically Windows XP or earlier – is now a potential victim.
As time progresses, it is also becoming apparent that despite the ransom demands, financial gain may, in fact, come second to disruption in terms of the perpetrators’ priorities.
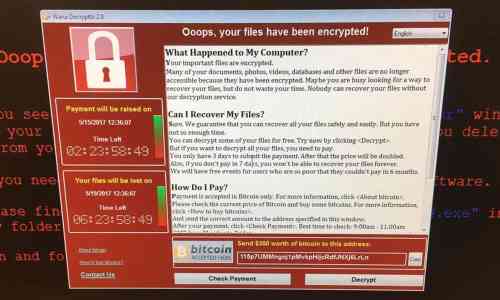
Sources suggest that from the 200,000 machines currently infected, hackers have accrued only $50,000 worth of Bitcoin.
Given the original demand of $300 per machine, they are $59,950,000 short, leading some to believe a previous threat to double price tag for regaining control could in fact occur.
“We think over the course of today as we approach the first deadline where fines double we will see a bigger increase (in bitcoin payments),” law enforcement support startup Elliptic CEO James Smith told CNBC.

Meanwhile, significant mainstream press exposure for Bitcoin has resulted in the usual deluge of misinformation hitting consumers.
British tabloid The Sun, writing about the virtual currency in light of the NHS stranglehold, even announced that Bitcoin “has no transaction fees.”
What do you think about Microsoft’s response to the WanaCrypt cyberattack? Let us know in the comments below!
Images courtesy of Twitter, Shutterstock, Associated Press