
A group called wallet.fail gave a presentation on how to hack cryptocurrency hardware wallets at the 35th Chaos Communication Congress. While all attack vectors required physical access, worryingly, the group demonstrated scraping the seed and PIN from Trezor RAM. So is there any way to truly protect your lovely bitcoin?
Lines Of Attack
The group found ways of hacking hardware wallets via four different methods; supply chain attack, firmware vulnerability, side-chain attack, and chip-level vulnerability. All techniques required access to the actual device, so if your wallet has never left your possession…then you could still be at risk from a supply chain attack.
Holographic security stickers apparently mean nothing, as they are easy to remove and replicate. But let’s assume your device is tamper-free.
Still Not Safe
The Ledger Blue outputs a slight RF signal when entering the PIN. Connect a USB cable and you have an antenna to transmit this across the room. You then become vulnerable to the $5 Wrench Attack.
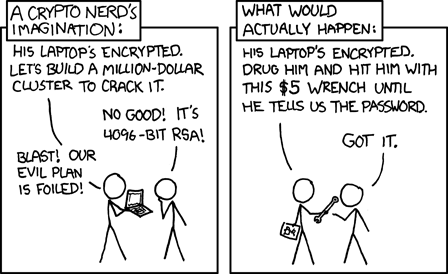
Even worse news for Trezor users. An attacker getting hold of the device (e.g. with a $5 wrench) can scrape your seed and PIN from RAM, unless you activated passphrase protection.
Trezor Passphrase Protection
(Disclaimer: Trezor recommends using the passphrase for advanced users only)
If you forget the passphrase, the funds protected by it are lost forever.)
Each passphrase creates a new unique wallet, acting as a 25th seed word. It can be any sequence of up to 50 ASCII characters – which means both numbers and letters can be used.
You must manually enable passphrase in the Advanced settings of the Trezor Wallet browser interface after each recovery process. To access the original wallet (without passphrase protection), leave the passphrase space empty.
By keeping a spoof wallet with negligible funds, you can even protect against $5 wrenches. Don’t be tempted to disable PIN protection too though, as a passphrase could be susceptible to a keylogger attack. D’oh!
A full description of how to enable Passphrase Encryption is explained in this YoutTube video.
Do you use a passphrase? What other security best-practices do you recommend? Share below!
Images courtesy of Randall Munroe xkcd.com. Used under the terms of the Creative Commons Attribution license, Shutterstock


















